Rapid 7 - Patch Tuesday - December 2024

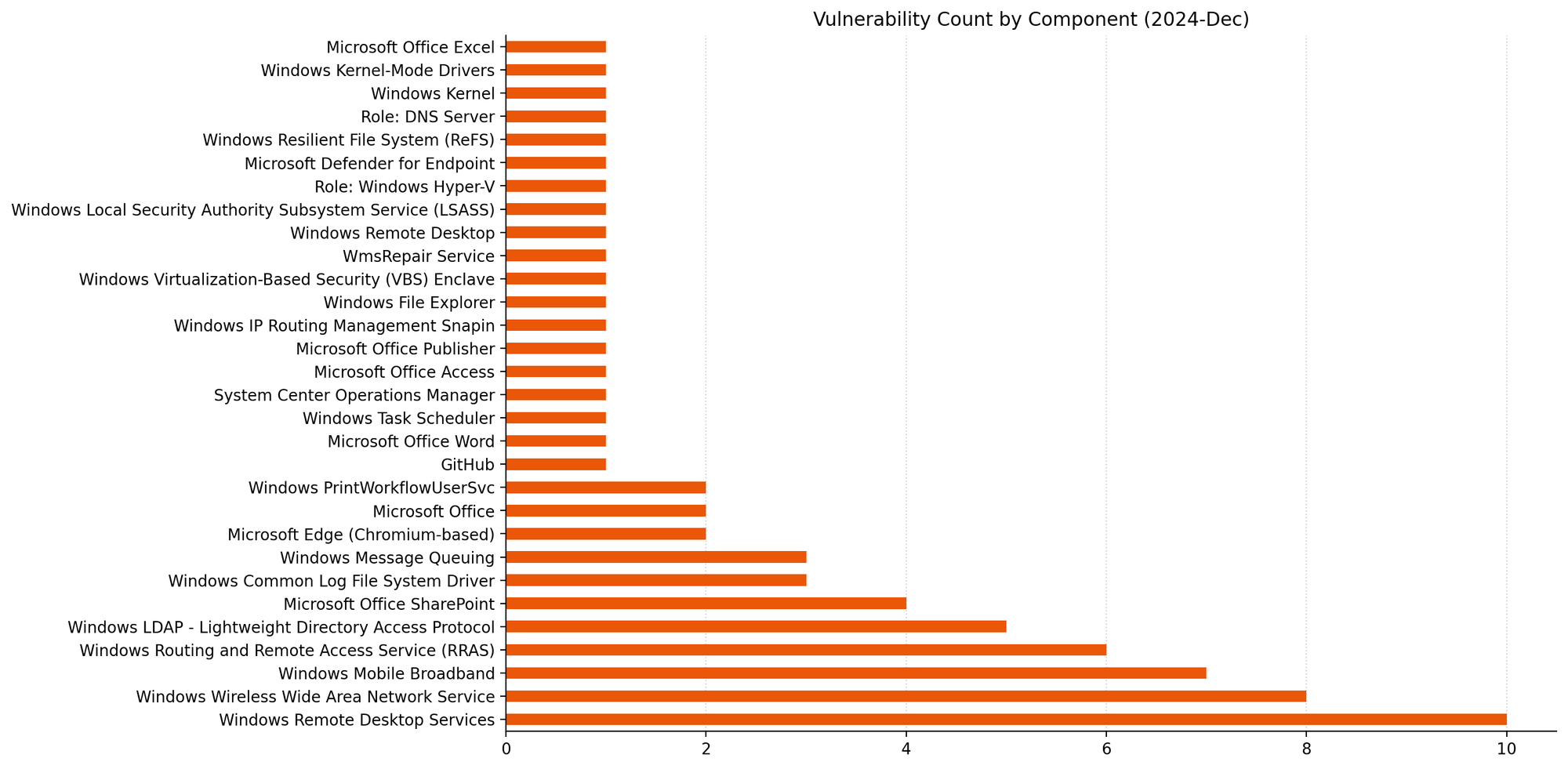
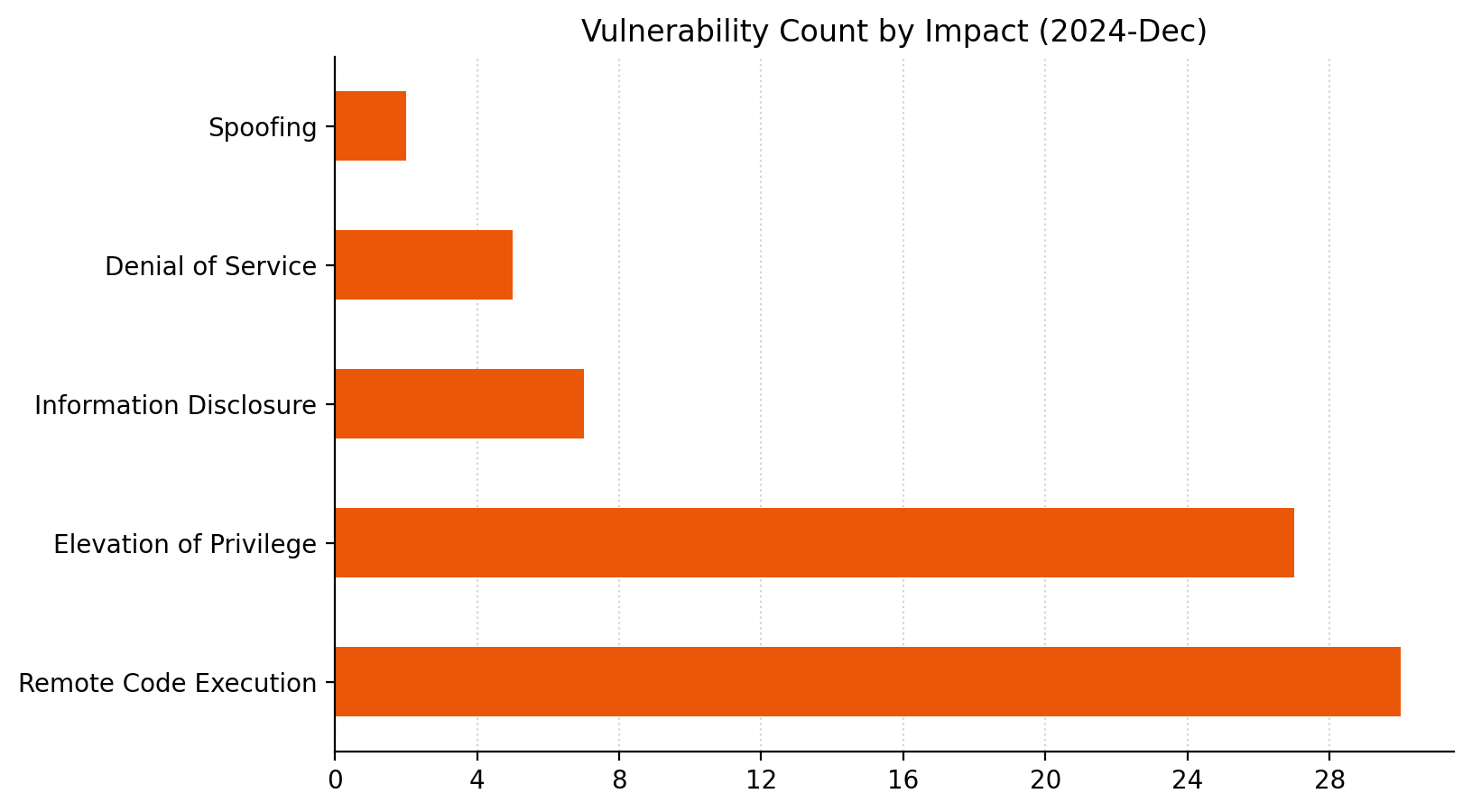
Microsoft is addressing 70 vulnerabilities this December 2024 Patch Tuesday. Microsoft has evidence of in-the-wild exploitation and public disclosure for one of the vulnerabilities published today, and this is reflected in a CISA KEV entry. For the third month in a row, Microsoft has published zero-day vulnerabilities on Patch Tuesday without evaluating any of them as critical severity at time of publication. Today sees the publication of 16 critical remote code execution (RCE) vulnerabilities, which is more than usual. Two browser vulnerabilities have already been published separately this month, and are not included in the total.
Common Log File System: zero-day EoP
This month’s zero-day vulnerability is CVE-2024-49138, an elevation of privilege vulnerability in the Windows Common Log File System (CLFS) driver, a general-purpose Windows logging service that can be used by software clients running in user-mode or kernel-mode. Exploitation leads to SYSTEM privileges, and if this all sounds familiar, it should.
There have been a series of zero-day elevation of privilege vulnerabilities in CLFS over the past few years. Past offenders are CVE-2022-24521, CVE-2023-23376, CVE-2022-37969, and CVE-2023-28252; today’s addition of CVE-2024-49138 is the first CLFS zero-day vulnerability which Microsoft has published in 2024. Although the advisory doesn’t provide much detail on the means of exploitation, the weakness is CWE-122: Heap-based Buffer Overflow, which most commonly leads to crashes/denial of service, but can also lead to code execution.
Ransomware authors who have abused previous CLFS vulnerabilities will be only too pleased to get their hands on a fresh one. Expect more CLFS zero-day vulnerabilities to emerge in the future, unless Microsoft decides to perform a full replacement of the aging CLFS codebase instead of offering spot fixes for specific flaws. Patches are available for all versions of Windows.
Groups of critical RCE
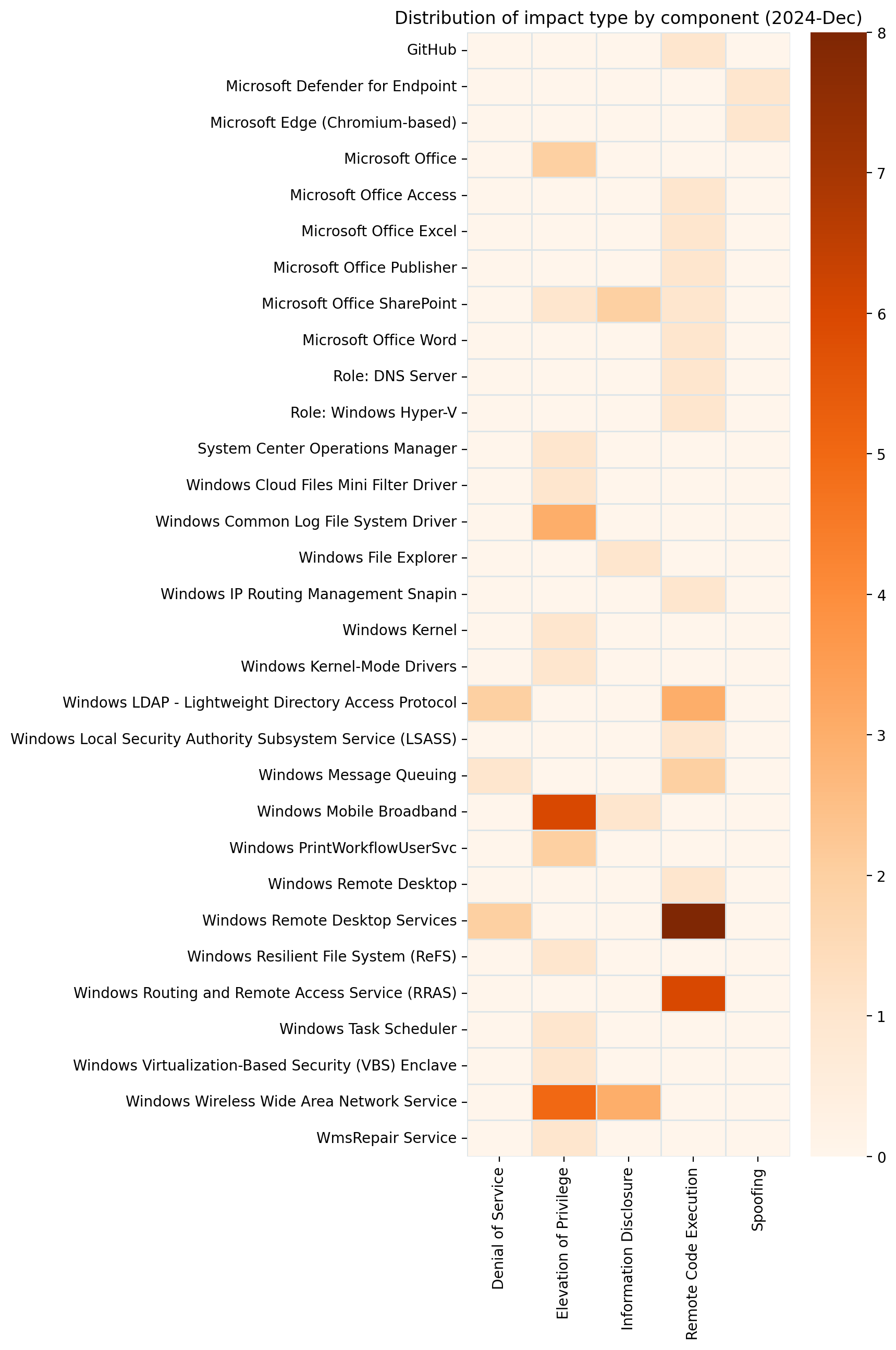
Patterns emerge when we consider the 16 critical RCE vulnerabilities published today as a whole, which might somewhat reduce the level of alarm that unusually large number might otherwise cause weary defenders.
LDAP: critical RCE
A trio of Windows LDAP critical RCE vulnerabilities receive patches this month, including CVE-2024-49112, which has a CVSSv3 base score of 9.8, which is the highest of any of the vulnerabilities which Microsoft has published today. Exploitation is via a specially crafted set of LDAP calls, and leads to code execution within the context of the LDAP service; although the advisory doesn’t specify, the LDAP service runs in a SYSTEM context. Microsoft advises defenders who still permit domain controllers to receive inbound RPC calls from untrusted networks or to access the internet to stop doing that.
LSASS: critical RCE
Another potential cause for concern this month: CVE-2024-49126 is a critical RCE in the Local Security Authority Subsystem Service (LSASS). Exploitation could potentially be carried out remotely, and the attacker needs no privileges, nor does the user need to perform any action; the only silver lining is that an attacker must win a race condition. Although the advisory says that code execution would be in the context of the server’s account, it might be safest to assume that code execution would be in a SYSTEM context.
Hyper-V: container escape
CVE-2024-49117 describes a container escape for Hyper-V; exploitation requires that the attacker make specially crafted file operation requests on the virtual machine (VM) to hardware resources on the VM, which could result in remote code execution on the hypervisor. The FAQ on the advisory sets out that no special privileges are required in the context of the VM, so any level of access is enough to break free from the VM. We also learn that the container escape could be lateral, where an attacker moves from one VM to another, rather than to the hypervisor.
Remote Desktop Services: 8 critical RCEs
All eight critical RCE vulnerabilities in Remote Desktop Services published today (e.g. CVE-2024-49106) share a number of similarities: they have identical CVSS vectors, exploitation requires that an attacker win a race condition, and the same research group is credited in each case.
Microsoft lifecycle update
There are no significant Microsoft product lifecycle transitions this month.
Summary charts
Summary tables
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49041 | Microsoft Edge (Chromium-based) Spoofing Vulnerability | No | No | 4.3 |
| CVE-2024-12053 | Chromium: CVE-2024-12053 Type Confusion in V8 | No | No | N/A |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49063 | Microsoft/Muzic Remote Code Execution Vulnerability | No | No | 8.4 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49068 | Microsoft SharePoint Elevation of Privilege Vulnerability | No | No | 8.2 |
| CVE-2024-43600 | Microsoft Office Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49069 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49142 | Microsoft Access Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49070 | Microsoft SharePoint Remote Code Execution Vulnerability | No | No | 7.4 |
| CVE-2024-49059 | Microsoft Office Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-49064 | Microsoft SharePoint Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2024-49062 | Microsoft SharePoint Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2024-49065 | Microsoft Office Remote Code Execution Vulnerability | No | No | 5.5 |
System Center vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49057 | Microsoft Defender for Endpoint on Android Spoofing Vulnerability | No | No | 8.1 |
| CVE-2024-43594 | System Center Operations Manager Elevation of Privilege Vulnerability | No | No | 7.3 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49093 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-49117 | Windows Hyper-V Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49106 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49108 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49115 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49119 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49123 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49132 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49116 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49076 | Windows Virtualization-Based Security (VBS) Enclave Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49074 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49114 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49075 | Windows Remote Desktop Services Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-49107 | WmsRepair Service Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2024-49097 | Windows PrintWorkflowUserSvc Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-49095 | Windows PrintWorkflowUserSvc Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-49073 | Windows Mobile Broadband Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-49092 | Windows Mobile Broadband Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-49077 | Windows Mobile Broadband Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-49078 | Windows Mobile Broadband Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-49083 | Windows Mobile Broadband Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-49110 | Windows Mobile Broadband Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-49094 | Wireless Wide Area Network Service (WwanSvc) Elevation of Privilege Vulnerability | No | No | 6.6 |
| CVE-2024-49101 | Wireless Wide Area Network Service (WwanSvc) Elevation of Privilege Vulnerability | No | No | 6.6 |
| CVE-2024-49111 | Wireless Wide Area Network Service (WwanSvc) Elevation of Privilege Vulnerability | No | No | 6.6 |
| CVE-2024-49081 | Wireless Wide Area Network Service (WwanSvc) Elevation of Privilege Vulnerability | No | No | 6.6 |
| CVE-2024-49109 | Wireless Wide Area Network Service (WwanSvc) Elevation of Privilege Vulnerability | No | No | 6.6 |
| CVE-2024-49087 | Windows Mobile Broadband Driver Information Disclosure Vulnerability | No | No | 4.6 |
| CVE-2024-49098 | Windows Wireless Wide Area Network Service (WwanSvc) Information Disclosure Vulnerability | No | No | 4.3 |
| CVE-2024-49099 | Windows Wireless Wide Area Network Service (WwanSvc) Information Disclosure Vulnerability | No | No | 4.3 |
| CVE-2024-49103 | Windows Wireless Wide Area Network Service (WwanSvc) Information Disclosure Vulnerability | No | No | 4.3 |
Windows ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49112 | Windows Lightweight Directory Access Protocol (LDAP) Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-49085 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49086 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49102 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49104 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49125 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49080 | Windows IP Routing Management Snapin Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49120 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49128 | Windows Remote Desktop Services Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49126 | Windows Local Security Authority Subsystem Service (LSASS) Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49127 | Windows Lightweight Directory Access Protocol (LDAP) Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49122 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49118 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49124 | Lightweight Directory Access Protocol (LDAP) Client Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-49072 | Windows Task Scheduler Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49138 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Yes | Yes | 7.8 |
| CVE-2024-49088 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49090 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49079 | Input Method Editor (IME) Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49129 | Windows Remote Desktop Gateway (RD Gateway) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-49121 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-49113 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-49096 | Microsoft Message Queuing (MSMQ) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-49089 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 7.2 |
| CVE-2024-49091 | Windows Domain Name Service Remote Code Execution Vulnerability | No | No | 7.2 |
| CVE-2024-49084 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-49082 | Windows File Explorer Information Disclosure Vulnerability | No | No | 6.8 |
from Rapid7 Cybersecurity Blog https://blog.rapid7.com/2024/12/10/patch-tuesday-december-2024/
Comments
Post a Comment