Krebs - Further Down the Trello Rabbit Hole
Last month’s story about organizations exposing passwords and other sensitive data via collaborative online spaces at Trello.com only scratched the surface of the problem. A deeper dive suggests a large number of government agencies, marketing firms, healthcare organizations and IT support companies are publishing credentials via public Trello boards that quickly get indexed by the major search engines.
By default, Trello boards for both enterprise and personal use are set to either private (requires a password to view the content) or team-visible only (approved members of the collaboration team can view).
But individual users may be able to manually share personal boards that include personal or proprietary employer data, information that gets cataloged by Internet search engines and available to anyone with a Web browser.

David Shear is an analyst at Flashpoint, a New York City based threat intelligence company. Shear spent several weeks last month exploring the depths of sensitive data exposed on Trello. Amid his digging, Shear documented hundreds of public Trello boards that were exposing passwords and other sensitive information. KrebsOnSecurity worked with Shear to document and report these boards to Trello.
Shear said he’s amazed at the number of companies selling IT support services that are using Trello not only to store their own passwords, but even credentials to manage customer assets online.
“There’s a bunch of different IT shops using it to troubleshoot client requests, and to do updates to infrastructure,” Shear said. “We also found a Web development team that’s done a lot of work for various dental offices. You could see who all their clients were and see credentials for clients to log into their own sites. These are IT companies doing this. And they tracked it all via [public] Trello pages.”
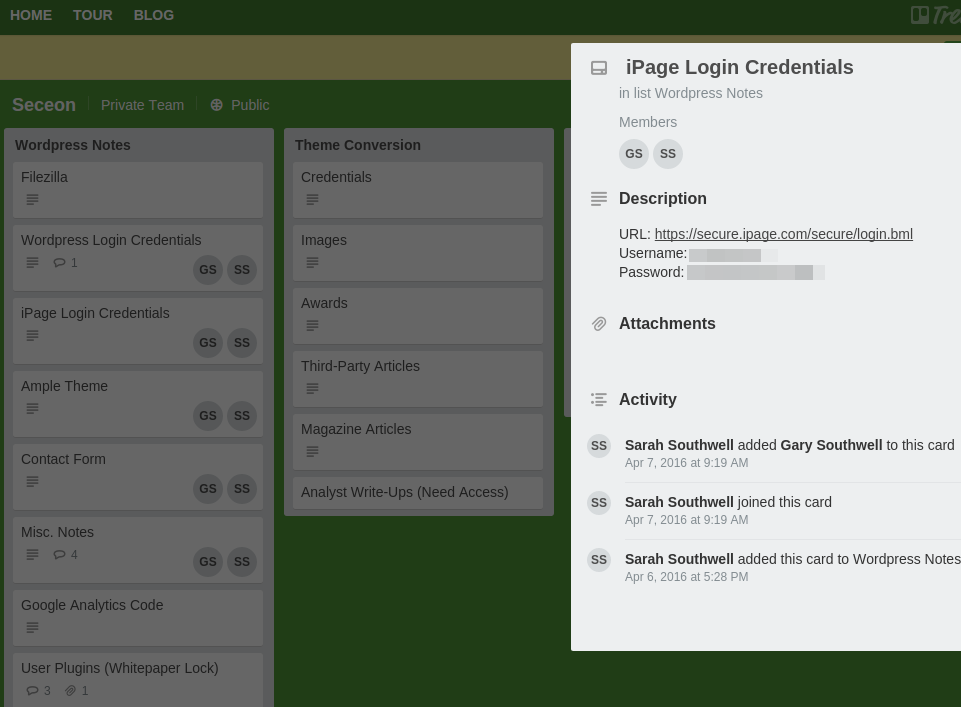
One particularly jarring misstep came from someone working for Seceon, a Westford, Mass. cybersecurity firm that touts the ability to detect and stop data breaches in real time. But until a few weeks ago the Trello page for Seceon featured multiple usernames and passwords, including credentials to log in to the company’s WordPress blog and iPage domain hosting.
Shear also found that a senior software engineer working for Red Hat Linux in October 2017 posted administrative credentials to two different servers apparently used to test new builds.
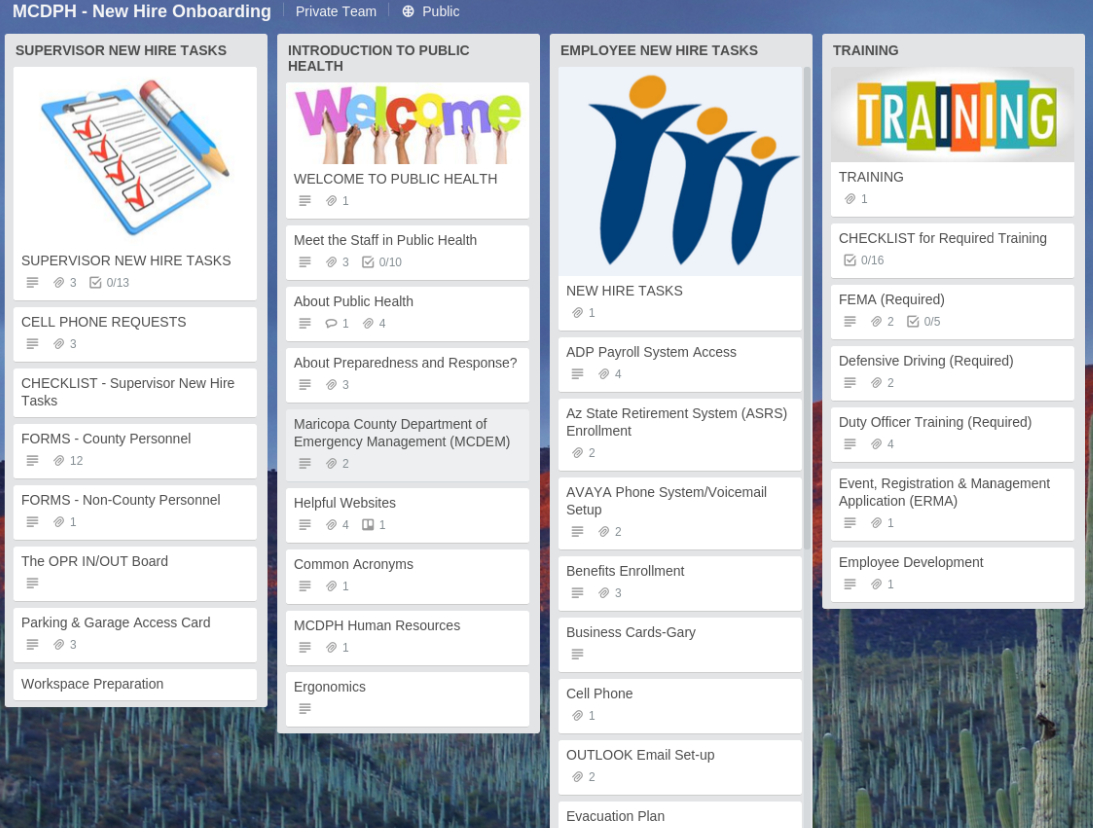
The Maricopa County Department of Public Health (MCDPH) in California used public Trello boards to document a host of internal resources that are typically found behind corporate intranets, such as this board that aggregated information for new hires (including information about how to navigate the MCDPH’s payroll system):
Even federal health regulators have made privacy missteps with Trello. Shear’s sleuthing uncovered a public Trello page maintained by HealthIT.gov — the official Web site of the National Coordinator for Health Information Technology, a component of the U.S. Department of Health and Human Services (HHS) — that was leaking credentials.
There appear to be a great many marketers and realtors who are using public Trello boards as their personal password notepads. One of my favorites is a Trello page maintained by a “virtual assistant” who specializes in helping realtors find new clients and sales leads. Apparently, this person re-used her Trello account password somewhere else (and/or perhaps re-used it from a list of passwords available on her Trello page), and as a result someone added a “You hacked” card to the assistant’s Trello board, urging her to change the password.
One realtor from Austin, Texas who posted numerous passwords to her public Trello board apparently had her Twitter profile hijacked and defaced with a photo featuring a giant Nazi flag and assorted Nazi memorabilia. It’s not clear how the hijacker obtained her password, but it appears to have been on Trello for some time.
Other entities that inadvertently shared passwords for private resources via public Trello boards included a Chinese aviation authority; the International AIDS Society; and the global technology consulting and research firm Analysis Mason, which also exposed its Twitter account credentials on Trello until very recently.
Trello responded to this report by making private many of the boards referenced above; other reported boards appear to remain public, minus the sensitive information. Trello said it was working with Google and other search engine providers to have any cached copies of the exposed boards removed.
“We have put many safeguards in place to make sure that public boards are being created intentionally and have clear language around each privacy setting, as well as persistent visibility settings at the top of each board,” a Trello spokesperson told KrebsOnSecurity in response to this research. “With regard to the search-engine indexing, we are currently sending the correct HTTP response code to Google after a board is made private. This is an automated, immediate action that happens upon users making the change. But we are trying to see if we can speed up the time it takes Google to realize that some of the URLs are no longer available.”
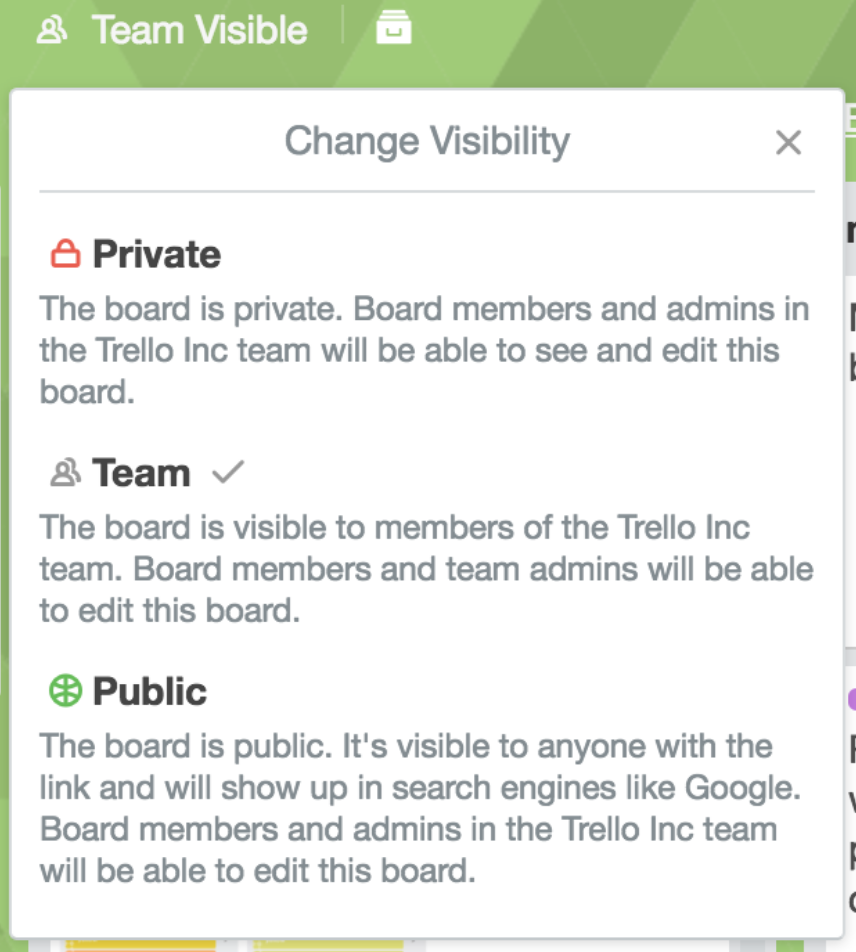
If a Trello board is Team Visible it means any members of that team can view, join, and edit cards. If a board is Private, only members of that specific board can see it. If a board is Public, anyone with the link to the board can see it.
Flashpoint’s Shear said Trello should be making a more concerted effort to proactively find sensitive data exposed by its users. For example, Shear said Trello’s platform could perform some type of automated analysis that looks for specific keywords (like “password”) and if the page is public display a reminder to the board’s author about how to make the page private.
“They could easily do input validation on things like passwords if they’re not going to proactively search their own network for this stuff,” Shear said.
Trello co-founder Michael Pryor said the company was grateful for the suggestion and would consider it.
“We are looking at other cloud apps of our size and how they balance the vast majority of useful sharing of public info with helping people not make a mistake,” Pryor said. “We’ll continue to explore the topic and potential solutions, and appreciate the work you put into the list you shared with us.”
Shear said he doubts his finds even come close to revealing the true extent of the sensitive data organizations are exposing via misconfigured Trello boards. He added that even in cases where public Trello boards don’t expose passwords or financial data, the information that countless organizations publish to these boards can provide plenty of ammunition for phishers and cybercriminals looking to target specific entities.
“I don’t think we’ve even uncovered the real depth of what’s probably there,” he said. “I’d be surprised if someone isn’t at least trying to collect a bunch of user passwords and configuration files off lots of Trello accounts for bad guy operations.”
from Krebs on Security https://krebsonsecurity.com/2018/06/further-down-the-trello-rabbit-hole/

Comments
Post a Comment